Network
From Wiki CEINGE
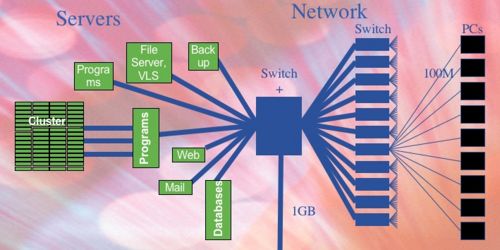
All the CEINGE areas are provided with wired and wireless internet connectivity, allowing internet access to all laboratories, service areas and offices; the wired connectivity is distributed by using Gbit fibers from one central area of the building to all peripheral areas and can be summarized as follow:
- Central network: One central network node provides connection to the peripheral nodes and connectivity to the internet; it is located in the server room where all the computing servers can connect redundantly to it by using ethernet connectivity up to 2 Gbit/s.
- Peripheral network: the central network is distributed in all the main areas of the institute by other perpheral network devices, mounted in 12 racks providing ethernet connection to the clients; the phisical network is further divided in functional areas, using virtual LANs, allowing client grouping and low level isolation between groups of computers, for security and network manageability.
- External connectivity: the central network is also responsible for the external connectivity to the internet and is based on a connection hosted by the close Faculty of Medicine; from there, a direct connection to the central network of the University of Naples Federico II, allows access to the research network (GARR) through a fiber at 1Gbit/s.
- Client connectivity: finally the desktop clients can be connected to the network by using wired and wireless connection; in the first case the clients need to be equipped with a fast ethernet card and properly configured by the system administrator according to the assigned VLAN. The IP configuration is managed by the system administrator and can be required by using the online form.
- Wireless network: In case of wireless connection, the clients need to be equipped with a wireless interface and to be configured to securely access the network, through authentication. All the main areas are covered and the connection speed to the main network can reach 54Mbit/s according to the 802.11g standard. See in detail how to configure it.
[edit] Network services
Almost all network services work transparently to the user but are needed to guarantee the correct functionality of a complex network architecture, offering different services and reaching appropriate levels of security. Network services can be grouped in different categories as explained in the following sections:
[edit] Base network services
- DNS
- A local DNS service is available to resolve all the ceinge network addresses belonging to the ceinge domain (ceinge.unina.it). It acts as a master DNS, propagating its information to the internet through the unina DNS servers.
- DHCP
- Most of the clients obtain the ip configuration dynamically by a dedicated static dhcp server working on all the networks configured in all the institute areas; it responds to the ip requests of the clients if its physical MAC address is registered; to request an IP address please use the online form.
- NAT
- The clients very often doesn't require to be on the public internet; so, they often work by using private addresses translated by the NAT server to a unique public ip address. This way, less number of limited public ip addresses are occupied and more security is achieved thanks to the isolation between networks.
- VPN
- A service of Virtual Private Network is configurable to allow people to join the ceinge network from outside the internet and allowing to use the internal services as local.
- RADIUS
- It responds to the access requests to use network services, such as wireless; this way, it provides controlled access to the network services and allow monitoring of malicious connection attempts.
- LDAP
- It is a directory service, used to manage user accounts centrally. It is used by all other IT services to guarantee authentication of the users and management of group of people.
[edit] Monitoring and management network services
Remote management is used to access and operate on computers reachable through the network; this kind of service is mostly dedicated to server machines and is based on secure connection using ssh or https protocols to remotely obtain a shell and to operate management via web interfaces. Monitoring is used to continuously check the functionality of the network as well as of the various systems.